Authenticity
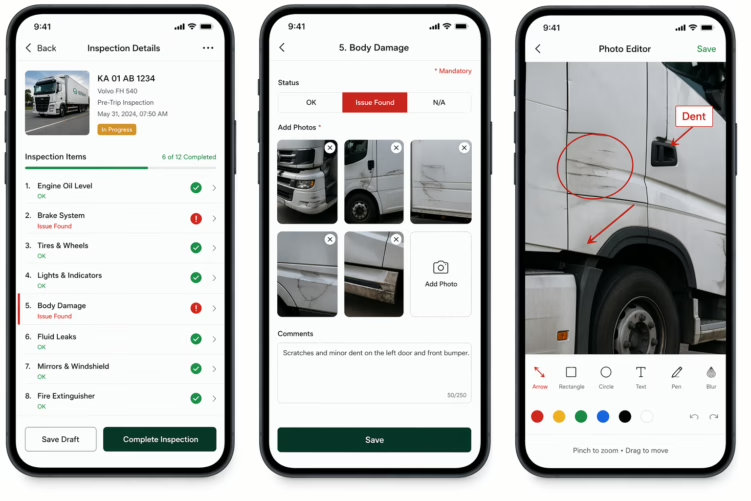
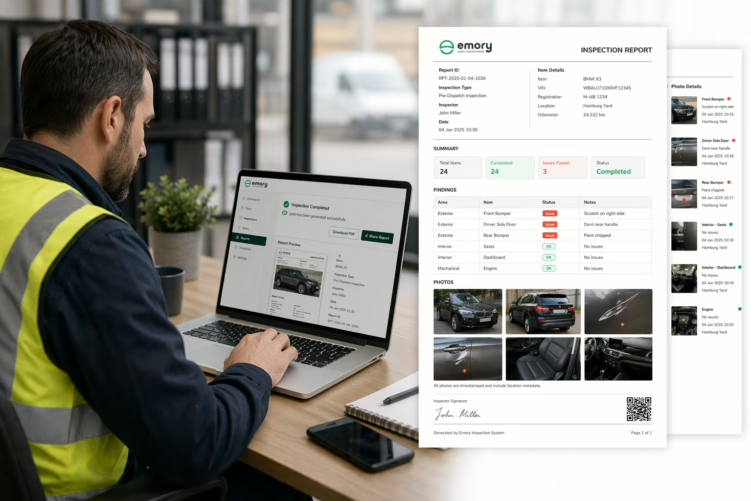
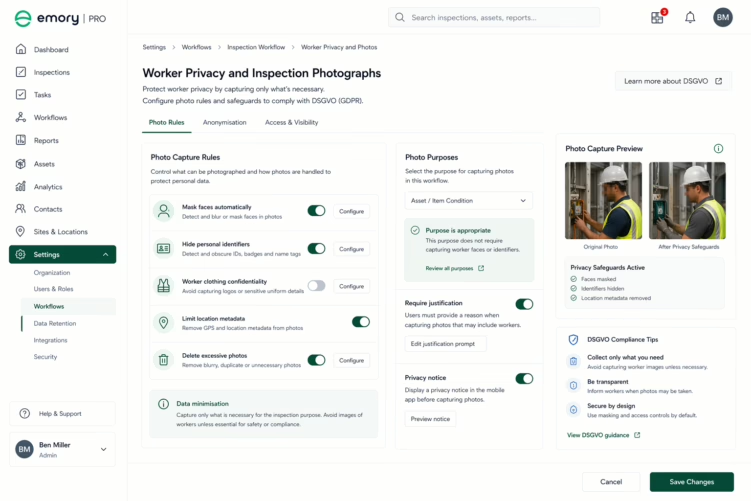
The photograph must be shown to be what it is claimed to be, an accurate representation of the subject at the claimed time and location, taken by the claimed person. Authenticity is established by demonstrating that the photograph was captured by a specific device, at a specific time and location, and has not been altered since capture.
In practice, authenticity is challenged by asking: could this photograph have been taken at a different time or location? Could it have been edited? Could it have been produced by someone other than the claimed photographer? If these questions cannot be answered from the photograph’s metadata and chain of custody, the photograph’s authenticity is open to challenge.
Integrity
The photograph must be shown to be unaltered from the moment of capture. Digital photographs are easily edited, exposure, colour, cropping, and even content can be modified without obvious trace. A photograph’s integrity is established by demonstrating that the image file has not been modified since capture.
Integrity is technically established through cryptographic hash functions, a mathematical fingerprint of the file that changes if the file is altered. If the hash value at the time of capture matches the hash value at the time of presentation, the file has not been altered. Most standard photograph workflows, capture, transfer, email, download, do not preserve or record hash values, making integrity verification impossible after the fact.
Provenance
The photograph must have a documented chain of custody from capture to presentation. This means knowing who took the photograph, what device was used, where and when it was captured, where it was stored, who had access to it, and how it came to be in its current location.
Provenance is broken by any gap in the chain, a photograph uploaded from a personal camera roll, transferred via personal messaging app, or stored in a personal cloud account that the organisation does not control introduces gaps that an opposing party can exploit.