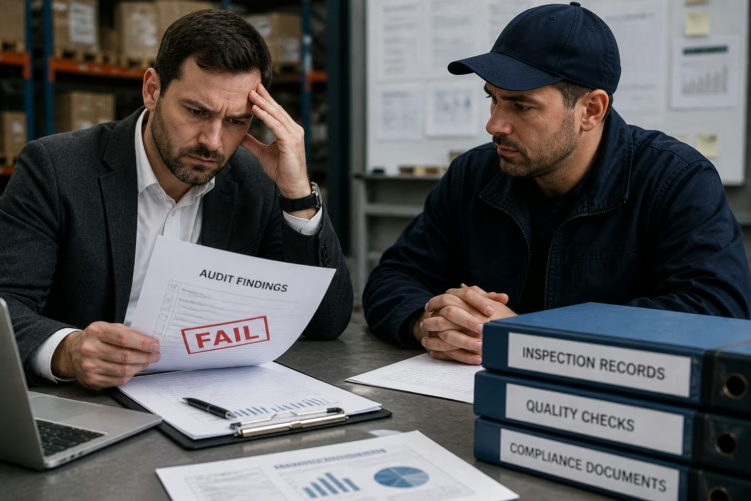
Audit-ready inspection evidence is not produced by conducting better inspections. It is produced by designing inspection systems that capture, structure, and preserve data in a form that meets the evidential requirements of audits, disputes, and regulatory reviews organisations may face.
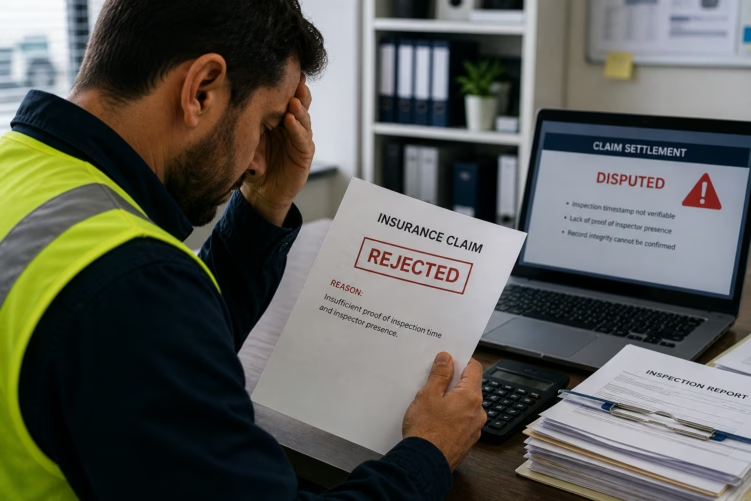
At Emory Pro, we have seen this repeatedly. Teams invest in better processes, but still fail audits because their inspection data lacks the structure, metadata, and integrity required.
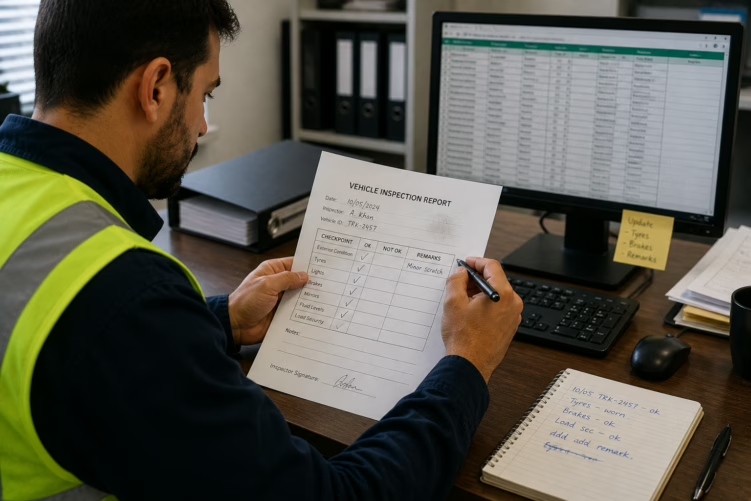
The distinction matters. An organisation can have highly competent inspectors, thorough checklists, and a genuine commitment to quality, and still produce inspection records that fail an audit.
That’s why we focus on building a digital inspection app and quality control system that ensures every inspection automatically becomes audit-ready.